DNS
DNS — the Domain Name System, which translates domain names into IP addresses.
For example, when we type google.com in the browser, the browser connects to a public DNS server,
which returns google.com's IP address in response, allowing the browser to establish
a connection with google.com's server and continue all further communication using this IP address.
Problem
By default, DNS traffic is not encrypted, which means that the request sent to the DNS server is visible to everyone:
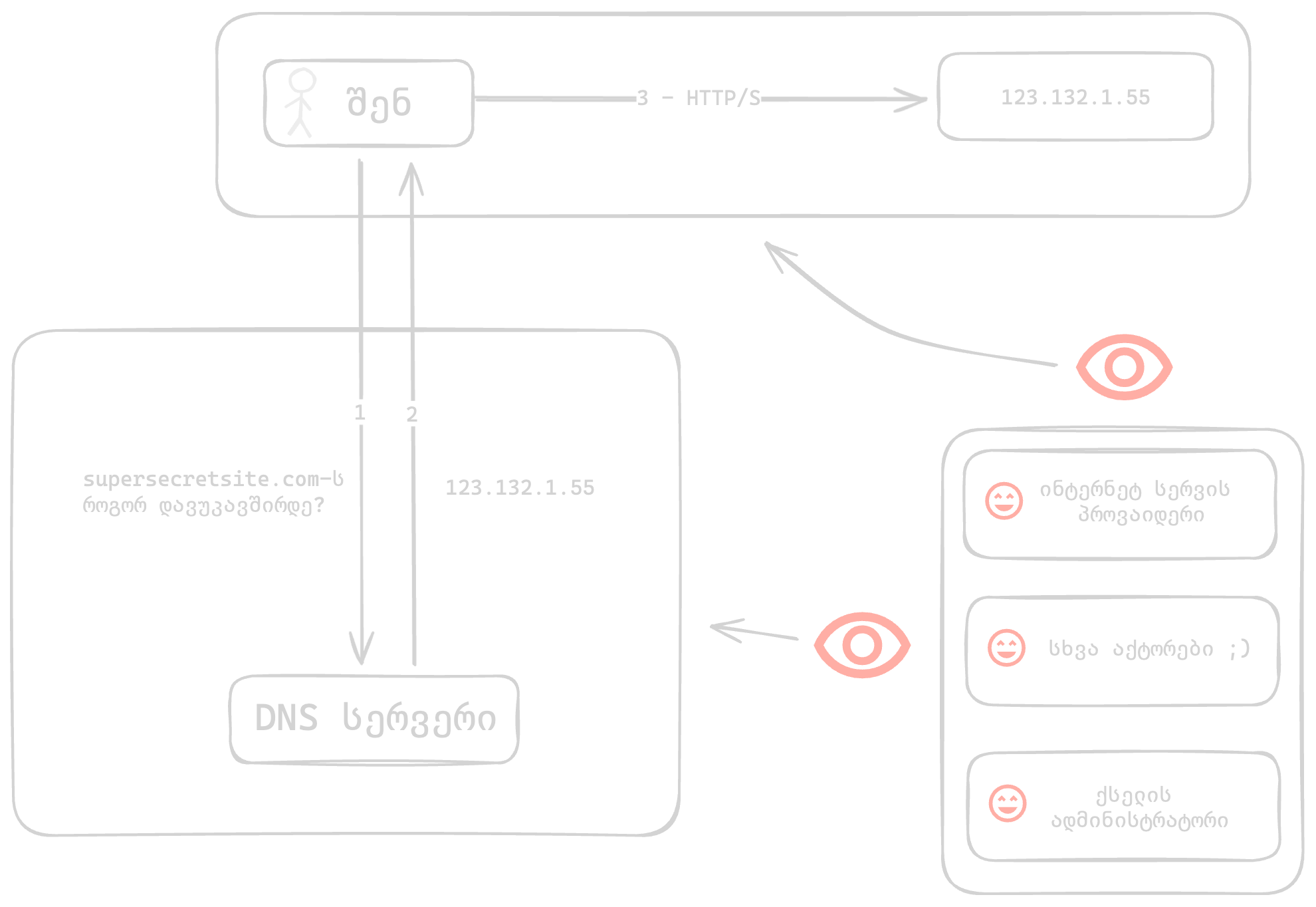
- The network administrator (e.g., the Wi-Fi owner)
- The internet service provider (which in many cases is also the owner of the DNS server the system connects to)
- Other entities involved in sending this request to its destination and back (e.g., internet service provider's partners)
All the entities listed above gain the following capabilities:
- Maintain records of when you visited a website or used an application
- Block a resource
Encrypted DNS¶
Solution
Encrypted DNS allows us to make these requests invisible to everyone except the DNS server owner itself.

Attention
By using Encrypted DNS, only the DNS request is hidden from the listed actors. After receiving the site's IP address from the DNS server, the connection from your device to that IP address will not be hidden.
To hide this request, you will need a VPN.
There are several common Encrypted DNS protocols:
- DNS over HTTPS (DoH)
- DNS over TLS (DoT)
- DNS over QUIC (DoQ)
DNS over HTTPS (DoH) is the simplest solution, because it "hides" alongside other standard internet traffic, making it difficult to block.
MacOS¶
On MacOS, enabling DoH is possible through a system profile.
However, applications can replace the parameters in the system profile with their own. This often creates the risk of DNS traffic leakage.
This applies to all browsers based on the Chromium engine (e.g., Chrome, Brave, Edge).
Because of this, the FOI system profile also contains browser settings, which instruct Chrome, Brave, Edge browsers to use system DNS, while for Firefox — it configures Cloudflare DoH directly in the browser.
Instructions:
- Install the FOI Security system profile
- Go to Settings > Network > Filters & Proxies and activate one of the following:
Available profiles
CloudFlare's DNS server. This server is standard and does not block ads or other domains.
- "CloudFlare DoH":
Enabled - Go to https://one.one.one.one/help in your browser and verify —
Using DNS over HTTPS (DoH) - Yes
AdGuard's DNS server. This server blocks a significant portion of ads, tracking, and phishing.
- "AdGuard DoH":
Enabled - Go to https://adguard.com/en/test.html in your browser and verify —
Protocol: DNS-over-HTTPS
iOS¶
On iOS, enabling DoH is possible through a system profile.
Instructions:
- Install the FOI Security system profile
- Go to Settings > General > VPN & Device Management > DNS and activate one of the following:
Available profiles
CloudFlare's DNS server. This server is standard and does not block ads or other domains.
- "CloudFlare DoH":
Enabled - Go to https://one.one.one.one/help in your browser and verify —
Using DNS over HTTPS (DoH) - Yes
AdGuard's DNS server. This server blocks a significant portion of ads, tracking, and phishing.
- "AdGuard DoH":
Enabled - Go to https://adguard.com/en/test.html in your browser and verify —
Protocol: DNS-over-HTTPS
Windows¶
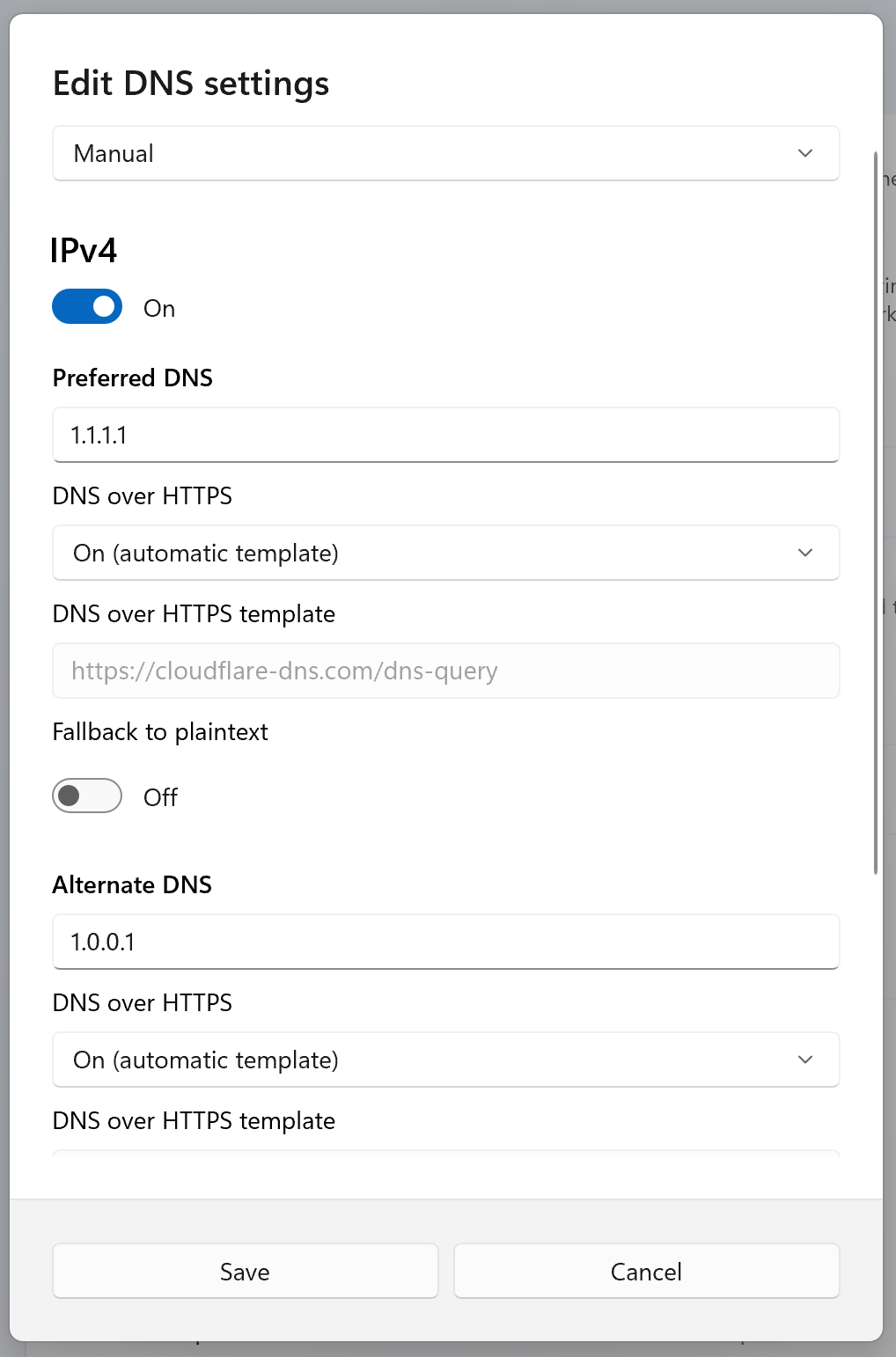
On Windows, enabling DoH is possible by changing network settings.
Instructions:
- Settings > Network & Internet > Wi-Fi
- Hardware Properties > DNS server assignment > Edit > Manual
- Select Manual from the dropdown list
- Enable IPv4
Available profiles
CloudFlare's DNS server. This server is standard and does not block ads or other domains.
- In Preferred DNS, enter 1.1.1.1
- In Alternate DNS, enter 1.0.0.1
- In DNS over HTTPS, select "On (automatic template)"
- DNS over HTTPS will automatically fill in:
https://cloudflare-dns.com/dns-query - Save
- Go to https://one.one.one.one/help in your browser and verify —
Using DNS over HTTPS (DoH) - Yes
AdGuard's DNS server. This server blocks a significant portion of ads, tracking, and phishing.
- In Preferred DNS, enter 94.140.14.14
- In Alternate DNS, enter 94.140.15.15
- In DNS over HTTPS, select "On (manual template)"
- In DNS over HTTPS, enter:
https://dns.adguard-dns.com/dns-query - Save
- Go to https://adguard.com/en/test.html in your browser and verify —
Protocol: DNS-over-HTTPS
If you connect to the internet via cable, repeat the same steps but on the first step select Ethernet instead of Wi-Fi.
Windows settings example
Android¶
On Android, DoH only works with two DNS services that are hardcoded 3.
Instead of the standard 1.1.1.1, when using a different server, the system will use DoT (DNS-over-TLS) instead of DoH, which may often be blocked by the network administrator.
Instructions:
- Settings > Network & Internet > Private DNS > Private DNS Provider hostname:
cloudflare-dns.com - Go to https://one.one.one.one/help in your browser and verify — "Using DNS over HTTPS (DoH) - Yes"
Additional reading:
DNS over HTTPS and DNS over TLS - Mullvad
Help